Exclusive: Gen. Paul Nakasone says China is now our biggest cyber threat
For nearly six years, Gen. Paul Nakasone led two of the most powerful — and secretive — arms of American national security: the NSA and U.S. Cyber Command. One listens. The other talks back.
Under the first Trump administration, Cyber Command got something it never had before: the green light not just to defend, but to be particularly aggressive in offensive cyber operations.
It was a turning point — a move from playing goalie to taking the shot — and offensive cyber operations have a way of being signals in their own right.
Late last month, Nakasone sat down with the Click Here podcast. He’s one of the architects of America’s cyber offense and in the half a dozen times we’ve interviewed him, he’s always been cautious and on message.
But this time, more than a year out of the job, he told us we could ask him anything. So we did. About China. About AI. And about what the current Trump administration might mean for America’s digital defenses.
The interview took place before the Atlantic magazine published its article about being included in a Signal chat with national security officials who were discussing military operations in Yemen.
The interview has been condensed and edited for clarity.
CLICK HERE: You stepped down from your job at NSA and Cybercom about a year ago … what are you doing now?
PAUL NAKASONE: Well, I have a portfolio approach to life. Right now I'm spending about half my time with the Vanderbilt Institute of National Security. I'm also on the board of directors for OpenAI. I do public speaking and I also do some consulting work for various businesses.
CH: And do you still have a relationship with the government?
PN: I don't. I'm on a cooling-off period right now and I think after 37 years that’s good.
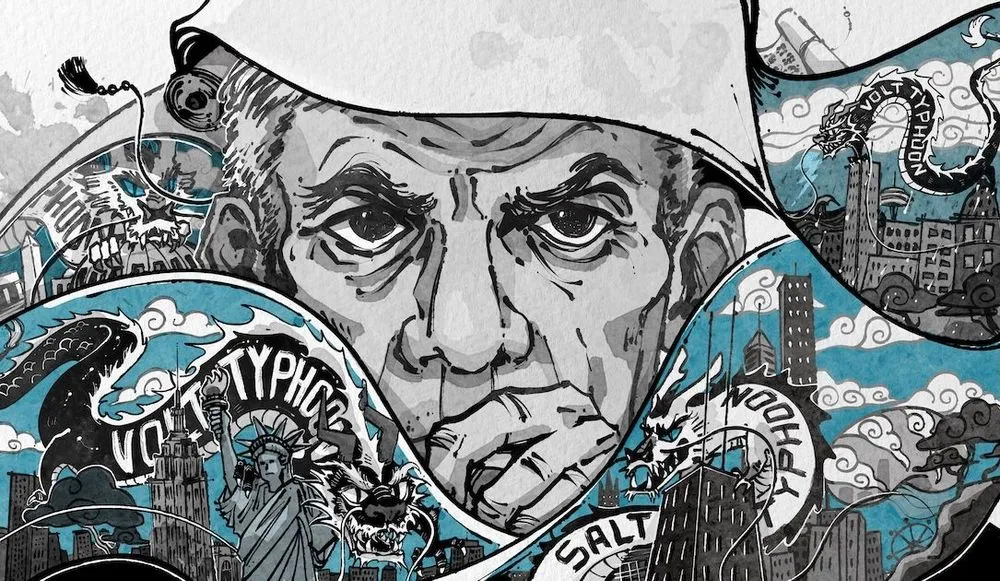
CH: You've said you worry that the United States is falling behind in cyberspace. … Is it the sheer prevalence of attacks that makes you say that? Is it that adversaries are stepping up with nation-state hacking groups like Volt Typhoon and Salt Typhoon? What are you seeing?
PN: In the year since I've left government, I would tell you that my focus is truly on The Chinese Communist Party, the People's Republic of China. They have separated themselves from other countries in terms of their capabilities.
Two years ago, we talked about [hacking groups like] Volt Typhoon and this idea of Chinese implanting malicious code in our critical infrastructure and key resources. This past year, we discovered them in our telecommunications companies.
Recently, I talked to the general manager of the Littleton Electric Water and Power District, right outside of Boston. He's a general manager there of a town of 10,000 and they just discovered the Chinese in their critical infrastructure.
What are Chinese hackers doing in Littleton, Massachusetts? I think that it's not just Littleton — I think there are many more [breaches] that we haven't found yet. But this gives you the sense of scale as to what my concern is.
"I think the priority should be to understand the scope and scale of what the Chinese are undertaking here. This is like nothing we have seen before."
— Paul Nakasone
When we take a look at Patch Tuesday, this idea of Microsoft being able to patch their vulnerabilities periodically, we now see the adversaries are into and being able to exploit those vulnerabilities within five days. And it takes businesses on average almost six months to find an intrusion into their networks and another two months to be able to take that malware or those attackers out of their networks.
That gives me a sense that we're behind. We're not keeping up. We have a very, very sophisticated nation-state that is continuing to use scope and scale. And the last part, I think, coming on to us is artificial intelligence, and as we think about that, I think we're not really sure: Is artificial intelligence going to be really powerful for the offense or perhaps for the defense? But those are the three concerns with cybersecurity.
CH: So what would you prioritize doing first?
PN: I think the priority should be to understand the scope and scale of what the Chinese are undertaking here. This is like nothing we have seen before. And I'm not sure that we have done a good job of talking about the challenge that this presents us with regards to our intellectual property, our personal data, our economic well being, and our national security.
The second thing is I think we have to have a much broader approach to how we defend ourselves in cyberspace. Everything has to get better — from our offensive capabilities to our defensive capabilities to our general understanding of the software. You know, after decades of talking about hygiene and patching, the software is not getting that much better and the attack surface is only growing.
CH: So let's talk a little bit about Volt Typhoon and Salt Typhoon [the names Western researchers use for specific Chinese nation-state operations]. … What are their intrusions in American networks telling us about China in cyberspace? It sounds like you think they’ve already replaced Russia as our major foe.
PN: Well, I, think they have. And again, this is the major change that I saw over the six years running NSA and Cyber Command: China has eclipsed all of our adversaries in terms of the scope and scale and now the sophistication of what they’re doing.
Consider Volt Typhoon. There is absolutely no intelligence to be gathered by putting malicious code in [critical infrastructure] networks. There's no intelligence to gather from the water in the United States or the water in different countries within the Indo-Pacific.
CH: Meaning this is clearly not an espionage operation.
PN: It's not espionage. This is not intended for espionage. This is intended to provide a capability at some point in the future that allows the Chinese to wreak havoc or spark a crisis [if they] enter a period of tension with the United States.
They want us to have to focus someplace else. … And look, it's very, very hard to detect someone who has stolen passwords or someone that has stolen credentials to get into a network or a data or a weapon system. And so as we look at that, we say, wow that's a sophistication that shows that the Chinese are continuing to get better.
"One of the challenges that we've had is that we have fallen behind with a deterrent approach to cyberspace."
And when it comes to Salt Typhoon’s [effort to hack into U.S. telecom companies], this was all about intelligence … getting into the networks and then being able to use incredible tools like large language models to be able to identify, and then be able to target specific people.
They were very purposeful in who they went after. Not only political figures, but the Department of Justice, the Federal Bureau of Investigation. Why is that? Wouldn't it be nice to know? Who might be under surveillance with regards to whom we might believe are Chinese espionage candidates within the United States or those that, you know, we have concerns about?
That's a level of insight that they were trying to gather. And so, I think, again, that shows a pretty broad scale. It shows the scope of being able to do this for intelligence. But also a sophistication of being able to not only use the incredible collection that you're getting, but also pair it with the analysis capabilities like large language models.
CH: When you talk about China getting into networks in case of a crisis … the most likely one on the horizon is some sort of conflict about Taiwan. … What’s the scenario with regard to Taiwan that worries you?
PN: Miscalculation. Remember back in 2001 when an American intelligence plane was clipped by a Chinese fighter. The American plane lands at Hainan Island. There's a series of days where there's negotiation. We finally get our crew back, the plane stays there.
Think if that happened today … if we had an American intelligence plane that went down today — think about the social media that is going to generate. Think of the interest, the impact in terms of driving us to perhaps a heightened state of concern with regards to our country, but also think about what it means in China as well and how that's messaged. Something like that becomes very difficult to work your way through that type of environment with clear thinking [in that backdrop].
Now we've heard about the Chinese dredging for Taiwan's cables. If we think about the fact that they're conducting live-fire exercises relatively frequently off the island of Taiwan. If we think about the fact that the Coast Guard of People's Liberation Navy is being much more aggressive in terms of what's going on. At some point in time, do we become just inured to it? And suddenly it's a crisis or a conflict that might be so quick that it might even catch us by surprise.
CH: During your confirmation hearings back in 2018, one of the things that you said at the time was that our adversaries don't fear us in cyberspace. Do you think that's still true? Is that why we're seeing this kind of proliferation that you're talking about?
PN: I think one of the challenges that we've had is that we have fallen behind with a deterrent approach to cyberspace. One of the things that the first Trump administration did was provide the policies and authorities that allowed us to be much more proactive — the persistent engagement that basically says that every single day, we're going to be active outside the United States, ensuring that our adversaries knew what was going on.
And it is more than just offensive cyber, it’s also what our legal system is going to do. It's also what the private sector does. It's also what our international partners are going to do. This becomes much more sophisticated as we think about what has to be done.
CH: Are you surprised we're finding ourselves here after all this time, that we're still this vulnerable?
PN: This is a very dynamic environment, technology-wise, talent-wise, tradecraft-wise. We have to be dynamic. And I think we've lost a bit of that dynamism over the past several years and we have to regain that.
CH: How we'd make sure that no new equipment has the same vulnerabilities that the old equipment had: Do you think this has been addressed in any serious way?
PN: I think that we have to address it in a different way. And let me give you an example. One of the things I've talked about is the idea of radical partnerships. The government has intelligence and information that should be shared. The private sector individuals and organizations have an ability to address the vast majority of the networks, the data, the cloud systems that they control.
And guess what? Academia has tremendous expertise that isn't being tapped right now — and when you bring those three together you can have some pretty significant advantages in terms of being able to get after the problems that we have today.
CH: Let's talk about how we’re seeing cyber operations jumping from non-kinetic — say just taking down a system — to zeros and ones actually destroying physical things. We’ve seen the beginnings of that in Ukraine … with wiper malware that was in their critical infrastructure … is this a trend?
PN: I think you've identified one of the key trends that we're going to learn from Russia-Ukraine and Israel-Hamas. Were any of us surprised in the fall of 2024 when a series of pagers and walkie talkies were exploding and suddenly took out the operational level of Hezbollah?
This is the example of where cyber becomes not just a means upon which we learn intelligence or are able to use disinformation, but it really becomes a kinetic capability that armies and future individuals will learn how to use. And so, think about where we're at today with the Internet of Things and how many things of our households and ourselves are connected to the Internet. This is a trend and it is going to continue.
CH: A few weeks ago, the Record broke a story about Secretary of Defense Pete Hegseth ordering a pause in planning for Cybercom's offensive operations against Russia. Should people's hair be on fire about that?
PN: I want to provide context about how this might happen. It doesn’t matter if it's the Trump administration, the Biden administration — my experience has been that administrations provide guidance to combatant commanders with regards to the operations that they conduct. This is what the policymakers do. This is civilian-controlled military.
Whether or not it was Trump One or President Biden, I received that guidance as well. And so when there's a sensitive visit, when there are negotiations ongoing, they'll say, we would like to pause these type of Title 10 [military] operations that the Department of Defense is responsible for. [Intelligence-gathering operations fall under Title 50 of the U.S. code.]
"What has surprised me the most about AI is the speed upon which it's moving."
Two parts that I think are important for us to think about. First of all, none of us saw the order. So there was a tremendous amount of churn with regards to what did it say, what it didn’t say, what can they do, what can't they do.
But the big piece is I read in there was that this did not impact the National Security Agency. This is our intelligence arm upon which we rely on for early warning. No one's better than NSA. And so that was an important piece. And I think the other piece that we have to keep in mind is if this is days, even a couple weeks — that the pause is not uncommon. If this is months, then it is uncommon.
It's a dynamic environment as you operate within cyberspace. Your vulnerabilities change. Your capabilities can change. Your adversaries change. And so, you'll have to, a lot of times, start again and say, OK, this is the vulnerability that we were trying to exploit. This was the capability we would develop — maybe it worked; maybe it doesn't work anymore. These are things that, over time, change. It's not like flying the same route into a target location in the Pacific or Europe. This is a space that's man-made and it changes pretty frequently: Something is taken offline, a capability doesn't work anymore, a number of things can really change the dynamics of what you can do.
CH: Over the past three months, the president has allowed the Department of Government Efficiency to fire a lot of people in the federal government. There have been changes in the military, reorganization of the Office of Net Assessments, generals removed, military lawyers replaced. … this goes beyond just picking your own team. What's your reaction to all of this, because this seems broader than that.
PN: My concern always is losing really good talent — as a former commander, as a former director, I want the best talent and that talent means that some of it you have to, you know, recruit from industry, some of it, you know, comes out of the college system, some of it requires you to retain the best folks that don't want to leave private industry.
I don't want something that's going to disrupt that. I don't want something that calls into question whether or not this is a good place to work. These are all elements of being able to keep really good talent. And so that's my concern. I think that as many of us have looked at it there's a better way probably to do this than perhaps blanket statement of it's just going to be probationary period folks that are coming in.
CH: While you were at NSA and Cybercom, I think you did a lot of educating of politicians, maybe even presidents, of why cyber is important. When it comes to cyber, where do you think the Trump administration is headed?
PN: I think the national security adviser, Mike Waltz, has laid out some of that in terms of it's going to be a much more aggressive approach to reestablish deterrence. I think there are two unspoken elements that I'm still waiting to see come out. So how do we deal with Salt Typhoon and Volt Typhoon?
How do we deal with the challenge of China today? In other pieces, how do we take the advantages that we have in artificial intelligence and make this a continued advantage for us. How do we have a national strategy to build what I think is the most important disruptive technology of this century?
CH: So you’re on the OpenAI board … how do you perceive your role there?
PN: I joined the board in June of 2024. It was the only board I really wanted to get on after I left government and I decided Open was something that I wanted to be a part of because I think it's that important to the future of our nation, and to the future of democracies so that’s why it's one of the things that I went after.
My role on the board is to be part not only of the board of directors, but also on the committee that looks at safety and security. So I'm bringing the perspective of having run the largest element of the U.S. intelligence community, having been in the meetings with our national security leaders in Washington, D.C., and also I think the perspective of running large organizations to, to how I might be able to help. And it is a very dynamic process.
CH: When it comes to cyber, is AI going to be all about defense or help with offensive operations?
PN: I think the jury's out. When I left NSA, I was convinced that this was going to be an offensive tool, that was going to be very, very impactful. Yet what we saw in the elections was AI’s defensive capabilities — and they are much better than what the offensive capabilities were.
I think it comes back to this: you have ideas, you have innovation, then implementation comes after that. Who ends up implementing the best defensive offensive capabilities has yet to be seen. I don't think anyone knows yet.
Here's what I would tell you though, what has surprised me the most about AI is the speed upon which it's moving. I remember in November of ‘22 when ChatGPT came on, we were so excited to be able to throw a question into the prompt and suddenly this very mediocre high school student would give you an answer that may or may not be true and sometimes hallucinated.
What have we seen since then? We have seen reasoning, we have seen deep research, we've seen multi-modality in terms of being able to look at a number of different capabilities that come in and feed this information.
We're looking at the ability to create pictures. This is really moving quite fast, and I think for me — I think about the future — perhaps faster than I anticipated when I left government service.
CH: Some people have said that AI is really good at spotting other AI … is that why it’s so good at cyberdefense?
PN: I think that's one of the things that we've been very effective at. I think the other piece is that, as a general matter, offense is hard. It's not easy. And there are a number of different variables that play into it. Perhaps the AI agents that are now being developed will be able to conquer some of that. I'm not sure.
CH: What have you seen in terms of our adversaries using AI?
PN: From what I’ve read the Wall Street Journal and, and other media that, yes, it is certainly being used. Here's the piece that I think is interesting: For our own intelligence community I think this is going to have an incredible impact in terms of something I know very well — language analysis. We're not going to need the same number of linguists that we hired previously. The translation capabilities have gotten much better.
Secondly, think about something like wargaming — this idea of doing a tabletop exercise. Who sat at the tabletop? Well, it's a bunch of these generals and admirals. Did they know anything? Well, maybe they knew a few things. But think about this. If you have someone that has read every single speech and every single writing of [Chinese] President Xi and then is able to provide an analysis of what he might do under a certain situation, think about that, how it changes our strategies, our templates of what we're going to do. Think about how it challenges and makes us think about risk in a different way.
"People say, 'Are you using DeepSeek?' No. Where is the data being stored? Do I want to be able to have a conscious feeling that my data is being protected? Is it going to be used for something that I don't want it to be used for?"
And the final piece is the amount of data that's resident today. I think it really calls into question how impactful human operations, human intelligence operations are going to be in the future. There's just too many cameras.There's too much spotting. There's too much ability for artificial intelligence algorithms to be able to identify someone now. And I think it really then becomes this idea of who has the signals intelligence capabilities, oh yeah, and who's got the space capabilities.
CH: So we've been writing a lot about Elon Musk's DOGE. These 50 or so employees who are in government systems using AI tools, in some cases adding code. Are you worried about that? Does that introduce another vulnerability attack surface for adversaries?
PN: Certainly. Certainly. I mean, I think that this is the challenge any time that you have networks that are being provided a certain amount of privilege by different users. You're going to have our adversaries look for ways upon which they can draft in behind them. I think this is a great concern. I've heard a lot about it and I'm not privy to the details in terms of how it was done, but just the description certainly gives me pause.
CH: So if DOGE staffers are installing AI software throughout federal systems to automate tasks, that’s objectively worrisome?
PN: There's a very, very detailed process upon which we go through in being able to add software to our networks. And I know at times it's very frustrating, but there's a reason because we have such a broad surface upon which our adversaries can impact it. There’s always a challenge when those steps are skipped.
CH: So, you're talking about a change control process?
PN: Change control process, you know, authority to operate. Those are processes that are in place right now that govern the way that we run our networks.
CH: So what engenders more concern: a short pause in offensive operations from Cybercom or staffers inside government networks messing around with code?
PN: All of that is a problem to some degree. You asked me the question with regards to outsiders being able to access a network. That concerns me. It's a near-term concern that I think that I would be very, very focused on with regards to what our adversaries are doing to try to leverage that.
CH: How should we be thinking about China's latest answer to AI: DeepSeek?
PN: Let's rewind the clock to January. After the inauguration on the 20th of January, day one, Sam Altman and Larry Ellison and Masayoshi Sun from SoftBank are in the Oval Office talking about a $100 billion called Stargate. Two days later, DeepSeek releases its R1. I'm sure that was just by chance. [Laughs]
I talked about the changes since even ChatGPT came out November ‘22. Think about the changes that we're seeing in 2025. This is how we have to think about it. And I come back to the idea of, so what are we going to do about it? I think we need a strategy for AI, something that gets along the ideas of data, that gets along the ideas of energy, that gets along the ideas of semiconductors, and importantly, talent. That's really the equation we've got to solve for the future.
CH: And what are you wrestling with when it comes to ethics in AI?
PN: Well, I think that the early piece that we have done a very good job about is how do we ensure that the models that are being released by this company truly are safe and secure, that the testing that has been done has been done well. But I think we're just at the early piece of being able to think about what is this type of technology going to have an impact on in terms of our medical capabilities, our educational capabilities, how is it going to impact our economy, particularly job displacement, how is it going to be utilized for good as opposed to being utilized by others for something that is less than good.
CH: You've said in the past that the U.S. needs to be first when it comes to AI and you're talking about how models have to be safe and secure. The Chinese seem to be less worried about that. Experts say DeepSeek doesn't have those guardrails so that if you were to say, type in, “teach me how to make a bomb” — it might well tell you how.
PN: It concerns me. It does. I mean, I think that's one of the first things that I think about. People say, “Are you using DeepSeek?” No. Where is the data being stored? Do I want to be able to have a conscious feeling that my data is being protected? Is it going to be used for something that I don't want it to be used for?
That concerns me. And so, I think we have to have this continued discussion with the broader public about the challenges. It's much in the same way we had talked about TikTok previously.
But I think that this again is one of those areas that we've got to step back and say, Hey, that's not that's not something we want to be able to support.
CH: Can you talk about AI’s role in something like generative targeting … how might it work?
PN: One of the things that we've learned from the Russia-Ukraine conflict: Electronic warfare still has an impact on drones and other types of capabilities in terms of their navigation systems, their targeting systems. And one of the things that has been proposed is wouldn't it be interesting if we had this type of capability that would be able to make decisions on its own.
When it was being jammed, it could turn left or it could turn right. It could discern a target. It wouldn't need necessarily a capability or a tethering back to a human. This is the challenge that we're operating in right now as we look at our adversaries. They have no problems with the absence of a human in the loop.
That is something that goes against all of our policies in the Department of Defense. There is always a human in the loop for critical and lethal targeting. I think that as we move on in the future, we're going to have to figure out what is the level of comfort we're going to have with the ability of these generative capabilities to make decisions.
Is it OK to make a decision on a lethal run? Perhaps not. Is it OK for it to make a decision within a, a network as we're trying to look for a vulnerability or patch of vulnerability? Do we always have to go back to, to have a human in the loop there? Again, I think that our adversaries are going to push us to areas that we're going to have to make very key decisions on.
CH: We have a lightning round … you ready?
PN: I'm ready.
CH: Okay. If your WiFi goes down, do you fix it yourself, or do you call IT?
PN: Both. I'll do the initial fixing, and then I'll call my IT component if I need it.
CH: Is that your wife?
PN: No. It's one of my very good friends.
CH: I'm in charge of IT in our household.
PN: Excellent. Maybe I’ll call you.
CH: Happy to help. If you could recruit any fictional character into cybersecurity, who would it be?
PN: Easy. It's got to be Captain America.
CH: Of course. I had a feeling you'd go with Captain America. What's the most unhackable thing you own?
PN: The pencil and paper that I write on every single day.
CH: Why do you use a pencil instead of a pen?
PN: Because I need to erase it.
CH: What is the best book on cyber?
PN: The one that influenced me the most was "Dark Territory." That really kind of excited me in terms of what was going on. That's changed much in terms of what's going on, but that's one that reminds me of kind of my past.
CH: Thanks so much for being with us.
PN: Thank you. It's always good to see you, and thanks a lot for your time.
Dina Temple-Raston
is the Host and Managing Editor of the Click Here podcast as well as a senior correspondent at Recorded Future News. She previously served on NPR’s Investigations team focusing on breaking news stories and national security, technology, and social justice and hosted and created the award-winning Audible Podcast “What Were You Thinking.”